Just How Managed Data Protection Safeguards Your Service From Cyber Hazards
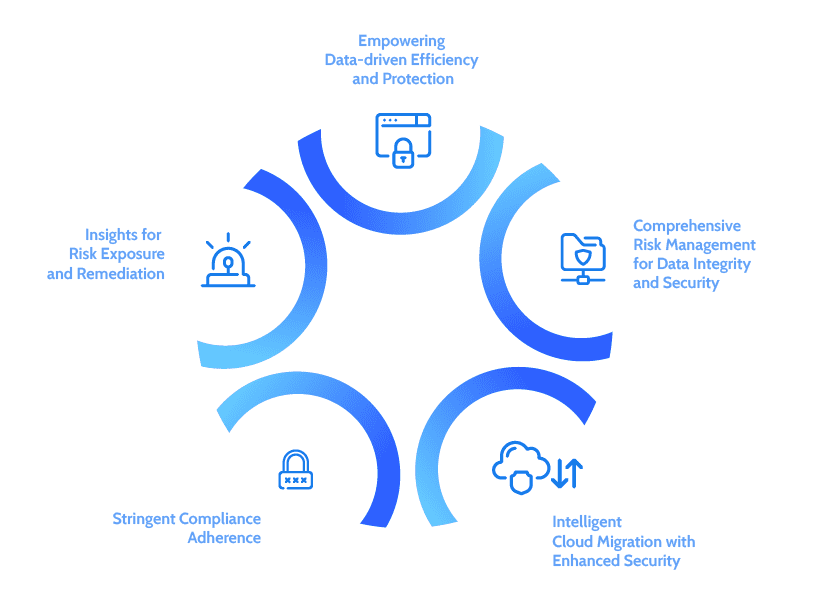
In a period where cyber hazards are significantly advanced, the value of taken care of information protection can not be overstated. Organizations that execute extensive safety and security measures-- such as data security, access controls, and continual tracking-- are better geared up to guard their delicate info. By contracting out these vital functions, services not only access to customized expertise yet additionally boost their ability to react to prospective susceptabilities. However, truth efficiency of these approaches often depends upon picking the ideal supplier and understanding the ramifications of conformity. What factors to consider should be focused on to make sure durable protection against evolving risks?

Comprehending Managed Data Defense
Managed data protection is an important component of contemporary cybersecurity approaches, with approximately 60% of companies choosing for such solutions to safeguard their vital information assets. This strategy entails outsourcing data defense obligations to specialized solution suppliers, allowing companies to concentrate on their core organization features while guaranteeing durable safety and security measures are in place.
The significance of handled information protection lies in its ability to supply extensive remedies that include information back-up, recovery, and danger discovery. By leveraging advanced modern technologies and experience, handled solution providers (MSPs) can implement aggressive steps that alleviate threats associated with information breaches, ransomware assaults, and various other cyber dangers. Such services are made to be scalable, fitting the progressing demands of organizations as they expand and adjust to new difficulties.
Moreover, managed data protection promotes compliance with regulative requirements, as MSPs typically remain abreast of the current industry criteria and practices (Managed Data Protection). This not just enhances the safety and security posture of an organization yet likewise infuses self-confidence amongst stakeholders regarding the stability and discretion of their information. Inevitably, comprehending taken care of data security is crucial for companies looking for to fortify their defenses against the ever-changing landscape of cyber hazards
Key Components of Information Protection
Efficient data defense techniques generally incorporate several vital components that operate in tandem to guard sensitive info. Primarily, data security is essential; it transforms legible data right into an unreadable layout, ensuring that even if unapproved accessibility occurs, the details continues to be secured.
Access control is one more important aspect, permitting companies to limit information accessibility to accredited personnel just. This reduces the risk of interior breaches and improves responsibility. Routine data back-ups are vital to ensure that information can be recovered in the event of data loss or corruption, whether due to cyberattacks or unintentional removal.
Following, a robust safety and security policy should be developed to lay out treatments for data taking care of, storage, and sharing. This policy must be consistently updated to adapt to developing threats. Additionally, continual monitoring and bookkeeping of information systems can identify anomalies and possible breaches in real-time, assisting in swift feedbacks to risks.
Benefits of Managed Solutions
Furthermore, took care of solutions help with positive surveillance and risk discovery. MSPs make use of advanced innovations and devices to continuously keep an eye on systems, making certain that abnormalities are determined and addressed before they escalate into serious problems. This aggressive strategy not just decreases feedback times yet additionally reduces the possible effect of cyber occurrences.
Cost-effectiveness is one more key advantage. By contracting out information defense to an MSP, organizations can avoid the substantial costs related to in-house staffing, training, and technology investments. This enables firms to allocate sources extra efficiently while still taking advantage of top-tier safety options.
Conformity and Governing Guarantee
Guaranteeing compliance with market laws and requirements is an important element of information protection that organizations can not forget. Governing frameworks, such as GDPR, HIPAA, and PCI DSS, enforce rigid requirements on just how organizations handle and secure sensitive information. Non-compliance can cause severe fines, reputational damages, and loss of customer trust fund.
Managed data security solutions help organizations browse the complicated landscape of compliance by implementing durable safety actions tailored to fulfill particular regulative requirements. These solutions offer organized methods to information security, gain access to controls, and routine audits, making certain that all procedures straighten with lawful responsibilities. By leveraging these handled solutions, organizations can preserve continual oversight of their data defense strategies, making certain that they adapt to evolving guidelines.
In addition, comprehensive reporting and paperwork supplied by taken care of data defense services function as important devices during conformity audits. These records demonstrate adherence to established requirements and procedures, providing assurance to stakeholders and governing bodies. Ultimately, purchasing handled information defense not only fortifies an organization's cybersecurity posture yet also imparts confidence that this link it is committed to maintaining compliance and regulatory assurance in a progressively intricate digital landscape.
Choosing the Right Service Provider
Selecting the right handled data defense company is vital for organizations intending to improve their cybersecurity frameworks. The primary step in this procedure is to examine the carrier's competence and experience in the field of information security. Try to find a supplier with a proven track record of efficiently guarding services versus different cyber dangers, along with knowledge with industry-specific regulations and conformity needs.
In addition, examine the series of services provided. An extensive company will certainly deliver not just backup and recuperation remedies however also aggressive risk detection, danger assessment, and case reaction abilities. It is vital to guarantee that the carrier utilizes sophisticated technologies, consisting of security and multi-factor verification, to secure delicate information.
Furthermore, consider the degree of client assistance and service degree contracts (SLAs) supplied. A receptive assistance group can considerably affect your company's capability to recuperate from cases swiftly. Testimonial endorsements and instance studies from existing customers to assess satisfaction and reliability. By thoroughly assessing these aspects, companies can make a notified choice and choose a service provider that aligns with their cybersecurity goals, ultimately enhancing their protection versus dig this cyber threats.
Verdict
Finally, handled information security serves as a vital defense versus cyber risks by employing durable protection measures, specific knowledge, and advanced modern technologies. The integration of comprehensive strategies such as data security, gain access to controls, and constant monitoring not only alleviates dangers but additionally ensures compliance with governing criteria. By contracting out these solutions, companies can improve their safety structures, helping with rapid recovery from data loss and over here fostering self-confidence amongst stakeholders when faced with ever-evolving cyber dangers.
In a period where cyber risks are increasingly innovative, the significance of taken care of data defense can not be overemphasized.The significance of taken care of information security exists in its capability to offer thorough options that consist of information backup, healing, and danger detection. Ultimately, understanding taken care of information protection is vital for companies seeking to fortify their defenses versus the ever-changing landscape of cyber risks.

In final thought, took care of information security serves as an essential protection against cyber hazards by employing robust safety actions, customized proficiency, and advanced technologies. Managed Data Protection.